This will be a living document in which I will document the Wireshark filters that I use most often. For those new to Wireshark, a filter is used to limit the number of displayed packets to help narrow down and more efficiently troubleshoot network issues by looking on only relevant packets.
I will use THIS capture as an example in all filters documented. You can download this packet capture and test the below filters yourself in Wireshark. This capture includes: visiting three websites and SMB (Windows file transfer over network) from one computer to another on the same network.
Single filters:
!(ipv6.version == 6) – exclude all IPv6 packets
– assuming you are troubleshooting IPv4 issues
ip – include only IPv4 packets
!(udp) – exclude all UDP packets
ip.src == 192.168.0.8 – include only packets with source IP 192.168.0.8
ip.dst== 192.168.0.8 – include only packets with destination IP 192.168.0.8
ip.addr == 192.168.0.8 – include only packets with source OR destination IP 192.168.0.8
ip.addr == 192.168.0.1/24 – include only local LAN packets, assuming local network is 192.168.0.1/24
Now we can combine some of the above as follows:
eth.dst == ff:ff:ff:ff:ff:ff && ip.src == 192.168.0.8 – include all broadcasts sent by source address 192.168.0.8
ip.addr == 192.168.0.9 && dns – include all DNS queries sent or received by 192.168.0.9
!(ipv6.version == 6) || !(udp) || eth.dst == ff:ff:ff:ff:ff:ff – exclude all IPv6, UDP and Broadcast packets
How do we come up with these complicated looking filters in the first place?
That’s easy.
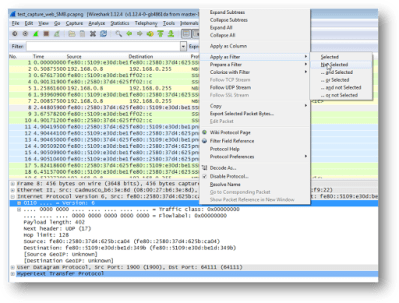
Simply right-click on the parameter you are interesting in including or excluding, then “Apply as Filter” and then choose one of the various logic based options. In the below example, we want to exclude all IPv6 packets, hence we chose the ‘Not Selected’ option, which populated our filter with the parameter:
!(ipv6.version == 6)
As you can see, the first screenshot has numerous IPv6 packets, and once the filter is applied, all IPv6 addresses are excluded (second screenshot). All of the above examples were created using the same right-click menu, with some minor modifications.
The best part is that the right-click method can be used with almost all parameters of the packet, so the options for filtering packets are virtually limitless.


Leave a comment